Wow! Let me catch my breath a second. It seems like we can’t go a week without another serious security bug being announced right now.
This week alone we’ve had 0-days in Windows, POODLE finally (hopefully) hammering the death nail into SSLv3 and Drupageddon - a pre-authentication SQL Injection vulnerability in the popular and awesome Drupal CMS. We even had bugs in the bug tracker and I’m not even going to talk about Shellshock again.
SSL - more trouble than it’s worth?
With a huge majority of sites shifting over to HTTPS - not because of security but because Google said it would give greater ranking to HTTPS websites - we could be forgiven for heading out to Starbucks without a copy of Wireshark. But alas no, don’t be put off by encrypted traffic because it turns out we can now decrypt big old chunks of it. With mainstream media reporting POODLE not long after Heartbleed it’s entirely possible that SSL/TLS is getting a bad name out there among normal, non-infosec people but that really wouldn’t be fair.
Heartbleed was a programming error in OpenSSL’s implementation and POODLE is a serious bug but in SSL version 3 - something that was deprecated over ten years ago and only used or supported in Internet Explorer 6. Given Microsoft themselves run a website dedicated to killing off the, very much legacy, Internet Explorer 6 it’s fair to say this really shouldn’t be that much of an issue for most people.
Don’t be daft
Transport layer security is still a cornerstone of secure communications over hostile networks, like the Internet. Any suggestion otherwise is misguided. We know it’s not perfect but it’s the best large-scale solution we’ve got right now. Like anything, it needs maintenance to ensure it remains fit for purpose.
It’s not *that* long ago that DES was the de facto encryption algorithm, we’ve come a long way since then.
What about Windows??
I’d bet my house that there is a very large stockpile of Windows 0-days out there, some in the hands of criminals, some researchers, some government agencies. The point is, as long as there is high profile software with widescale deployment there will be zero days. What is disappointing is how readily one zero day is all it takes to penetrate even large company defences. We saw it with the RSA breach and now with the Sandworm attacks against NATO.
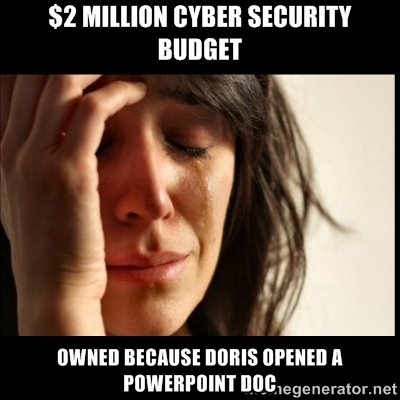
One click is all it takes
So often, one click is all it takes. The wrong Powerpoint document with an OLE exploit. The wrong Google Ad even, as was discussed this week at BlackHat EU in Amsterdam at a talk introducing Same Origin Method Execution - a neat attack against JSONP.
It’s a minefield for even the most hardened of security aware people to navigate the Internet safely. There is becoming a stronger argument everyday for browsing the Internet from a disposable machine with no JavaScript or plugins but that flies completely in the face of the amazing power the Internet has given us now. We want the full-on, multimedia, cloud-based, pick-up-where-I-left-off, face-in-a-smartphone-permanently-connected Internet, not the nineties-style text-based, 56k modem experience we used to have.
It comes at a price
But we can’t have it all. If we want state replication across multiple devices, centralised storage with always-on - or at least always switch-on-able - access with easy to use, swipeable UIs that our children understand intuitively we have to appreciate that we have exponentially increased our attack surface. Without taking additional steps we’re essentially baring our bum to the enemy and asking them to give it a big old slap.
There will be more bugs
If nothing else, all these bugs are raising awareness and that’s a great thing because when it comes down to it, for all the billion-dollar industry security has become with anti-virus giving way to total threat protection giving way to unified threat management, etc, etc it all comes down to Doris in Accounts.